-
The 90-Day Agent Identity Governance Plan
AI agents are moving fast, but governance is not keeping up today. This practical 90-day plan shows how to bring agent identities under control with ownership, least privilege, data-aware boundaries, and lifecycle discipline before hidden access, unmanaged connectors, and pilot magic turn useful automation into the next preventable security incident.
-

Shadow Agents Are the New Shadow IT
Shadow agents are the new shadow IT. This blog explains how unsanctioned agents, hidden connectors, and delegated access create new security risk, and why inventory, ownership, boundaries, and review are the practical controls that keep pilot magic from turning into production debt.
-
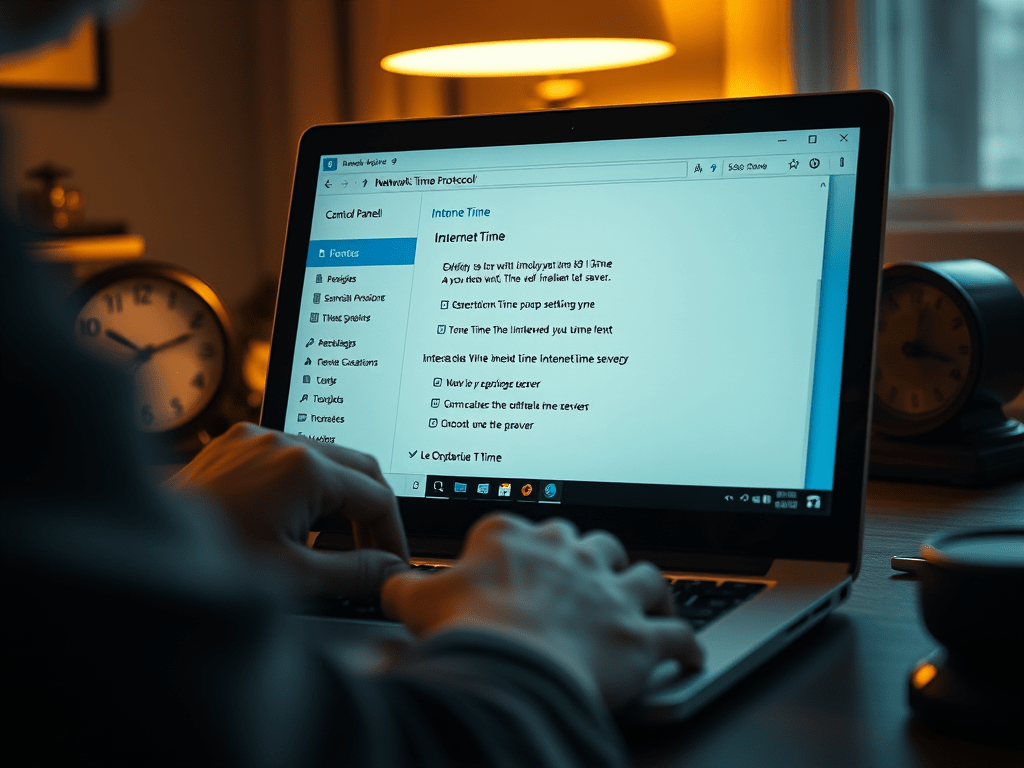
Configure Windows NTP Time Sync (Windows 10 / Windows 11)
I first wrote about this after getting smacked by what is, these days, an edge case IT problem: bad time sync, causing problems that looked like something else. This was at the start of COVID. Our team was all now working remotely, and one of our first in-person syncs during…
-

Use Device Groups to Automate Investigations in Microsoft Defender for Endpoint
Back in 2019, I wrote about using machine groups in Microsoft Defender ATP to automatically resolve investigations on selected systems. The core idea was simple: not every endpoint should be handled the same way, and security teams need a way to apply different remediation behavior to different classes of machines.…
-

Create an S-Mode Image of Windows 10
A Quick Guide for the IT Pro With the latest Windows 10 (Build 1809) release Windows 10 S was moved from an independent image on the installation media, to a mode you can apply to any SKU of windows 10. While in principle, this is a great addition to the…
-

Hybrid CI/CD with Azure Stack
Hybrid CI/CD with Azure Stack allows development teams to build, test, and deploy applications across on-premises infrastructure and Microsoft Azure using a consistent DevOps workflow. This guide explores how Azure Stack enables modern CI/CD pipelines, hybrid cloud development, and application delivery models that support both datacenter and cloud environments.
-

How To Differentiate with Microsoft’s Azure Stack
Azure Stack brings the Azure cloud model into your own datacenter, enabling hybrid cloud architecture where applications can run consistently across on-premises and public Azure. This post explores how Azure Stack helps organizations modernize infrastructure, meet regulatory and latency requirements, and differentiate by delivering Azure services locally while maintaining a…
-
Subscribe
Subscribed
Already have a WordPress.com account? Log in now.